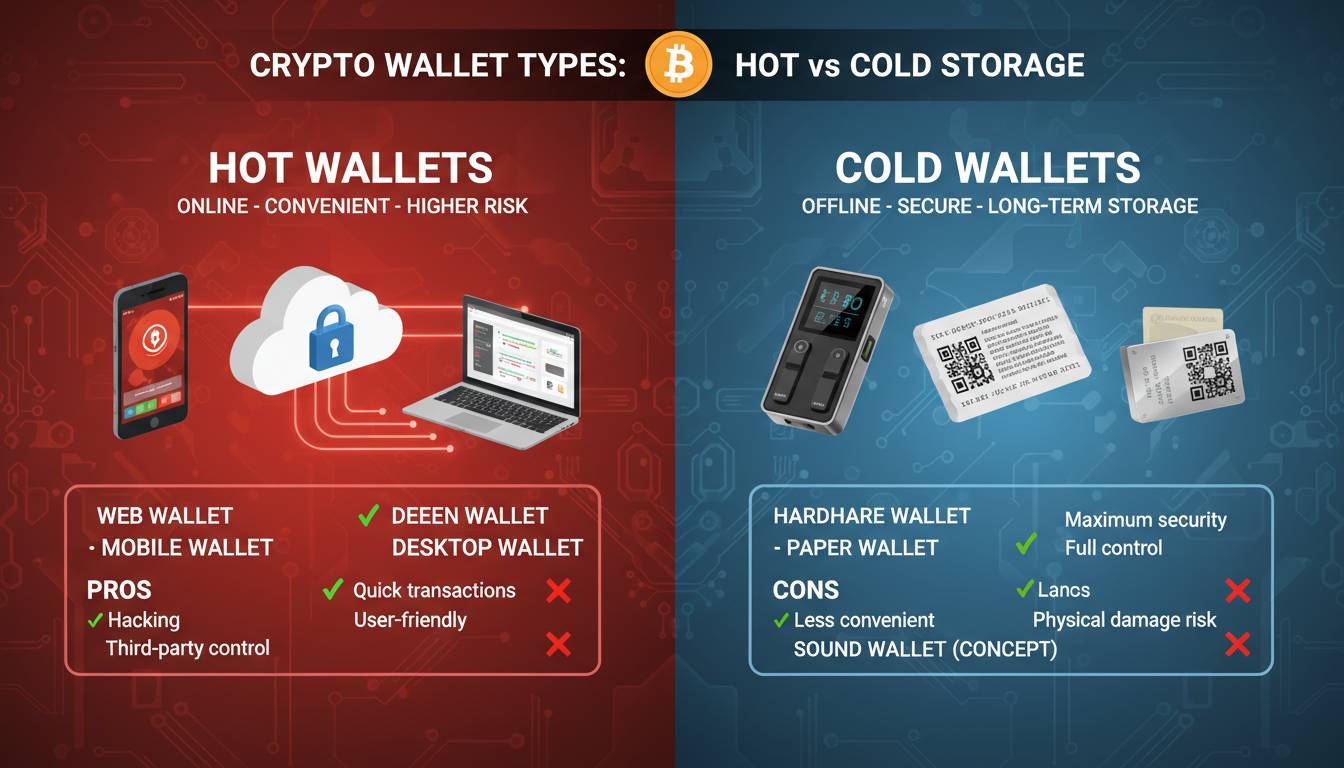
Cryptocurrency wallets serve as the fundamental gateway to the blockchain economy, yet millions of users remain uncertain about which type best suits their needs. With over 420 million cryptocurrency users worldwide as of 2024 and billions of dollars lost annually to hacks and scams, understanding the distinction between hot and cold storage has become essential for anyone holding digital assets. This comprehensive guide examines every major wallet type, evaluates security implications, and provides actionable recommendations based on your specific situation.
Key Insights
– Hot wallets account for approximately 80% of all cryptocurrency thefts despite holding only a fraction of total assets
– Cold storage solutions have grown 300% in adoption since 2020 among serious crypto holders
– The average crypto investor uses 2.3 different wallet types to balance accessibility and security
– Hardware wallet sales exceeded $1.2 billion globally in 2023, reflecting rising security awareness
What Are Cryptocurrency Wallets?
A cryptocurrency wallet does not actually store your digital coins. Instead, it holds the cryptographic private keys that prove ownership of your cryptocurrency and enable transactions on the blockchain. Think of your wallet address as a transparent safe where everyone can see your balance, while your private key serves as the combination that allows you to move those funds. This distinction matters because losing your private key means losing access to your funds permanently, with no customer service hotline to call.
The blockchain records all transactions permanently, but only those possessing the corresponding private keys can authorize movements from any given address. Modern wallets generate and store these keys using various methods, ranging from simple software files to specialized hardware devices. The security of your cryptocurrency ultimately depends on how well you protect these keys from unauthorized access.
Core Components
– Public address: Shareable string that receives funds (like an account number)
– Private key: Secret data that authorizes transactions (like a password)
– Seed phrase: 12 or 24-word backup phrase that regenerates your keys
– Wallet software: Interface that communicates with blockchain networks
Hot Wallets: Convenience at a Cost
Hot wallets remain connected to the internet continuously, enabling immediate access to your cryptocurrency for trading, spending, or frequent transactions. These wallets include browser extensions, mobile apps, and desktop software that maintain an active connection to blockchain networks through API connections or direct node communication.
The primary advantage of hot wallets centers on accessibility. If you trade cryptocurrency regularly, make purchases with crypto, or need to move funds quickly, a hot wallet provides the necessary speed. Major exchanges like Coinbase, Binance, and Kraken offer integrated hot wallets that allow seamless transfers between your holdings and trading platforms.
However, this connectivity creates inherent security vulnerabilities. Hackers increasingly target hot wallet users through phishing attacks, malware, and exchange breaches. The 2022 collapse of FTX demonstrated how centralized hot wallet custodians can fail catastrophically, leaving users unable to access their funds. Even well-secured platforms experience breaches regularly, with over $3.8 billion stolen from cryptocurrency platforms in 2022 alone.
Types of Hot Wallets
Browser Extensions: MetaMask, Rabby, and similar extensions connect directly to Web3 applications, making them essential for interacting with decentralized finance protocols and NFT marketplaces. These wallets store private keys encrypted within your browser, offering moderate security with maximum convenience.
Mobile Apps: Trust Wallet, Coinomi, and exchange apps provide smartphone access to your cryptocurrency. Mobile wallets include biometric security options like fingerprint or facial recognition, though phones remain vulnerable to malware and physical theft.
Desktop Software: Electrum, Exodus, and Atomic Wallet run as installed applications on your computer. Desktop wallets offer more robust features than mobile alternatives but require careful computer security practices to avoid malware infections.
| Hot Wallet Type | Security Level | Best For | Risk Factors |
|---|---|---|---|
| Browser Extension | Medium | DeFi users, NFT traders | Browser exploits, phishing |
| Mobile App | Medium-Low | Small holdings, daily use | Device theft, malware |
| Desktop Software | Medium-High | Active traders | Computer viruses, keyloggers |
| Exchange Wallet | Low | Beginners, small amounts | Platform hacks, insolvency |
Cold Storage: Maximum Security Solutions
Cold wallets keep your private keys completely offline, removing the attack surface that hackers exploit in hot wallet implementations. By generating and storing keys in environments disconnected from the internet, cold storage provides protection against remote attacks that have compromised countless hot wallets.
The fundamental security advantage stems from mathematical simplicity: a computer cannot be hacked if it never connects to a network. Cold wallet proponents often describe the approach as “air-gapped,” referring to the deliberate separation from online systems. Even sophisticated state-sponsored hackers face monumental challenges when attempting to access keys stored on devices with no network connectivity.
Recent years have witnessed remarkable growth in cold storage adoption among both individual investors and institutional holders. Grayscale Investments, one of the largest cryptocurrency asset managers, reportedly stores billions in cold storage facilities with multi-signature security protocols and geographic distribution across secure locations.
Types of Cold Wallets
Hardware Wallets: Devices like Ledger, Trezor, and Coldcard generate and store private keys within specialized secure elements. These USB-style devices require physical button confirmation for every transaction, eliminating the possibility of remote key theft. Hardware wallets cost between $50 and $300 and represent the most popular cold storage solution for individual investors.
Paper Wallets: Physical documents containing printed public addresses and private keys, paper wallets exist entirely outside digital systems. While extremely secure against remote attacks, paper wallets face risks from physical damage, loss, and human error in key transcription. Most security experts now recommend hardware wallets over paper alternatives for most users.
Steel Wallets: Companies like Cryptosteel and Billfodl offer fireproof, corrosion-resistant metal plates for seed phrase backup. These solutions protect against physical disasters that might destroy paper wallets, though they still require secure physical storage.
| Cold Storage Type | Security Level | Best For | Considerations |
|---|---|---|---|
| Hardware Wallet | Very High | All serious holders | Device cost, learning curve |
| Paper Wallet | High | Long-term storage | Physical vulnerability |
| Steel Backup | High | Disaster protection | Requires separate storage |
| Multi-signature | Very High | Large holdings, organizations | Complexity, coordination |
Security Comparison: What the Data Shows
Security comparisons between hot and cold storage reveal stark differences in vulnerability profiles. Chainalysis research indicates that 80% of cryptocurrency thefts target hot wallet infrastructure, with centralized exchanges bearing the majority of losses. Conversely, cold storage solutions have experienced remarkably few successful attacks, with most losses resulting from user error rather than security failures.
The 2021 hack of Poly Network demonstrated both the promise and peril of different approaches. Attackers exploited a vulnerability in cross-chain bridge infrastructure—a hot wallet environment—to steal $610 million in cryptocurrency. However, the attacker ultimately returned most funds, partly due to the transparency of blockchain transactions that made hiding impossible. This incident illustrates how even sophisticated hot wallet systems can be compromised, while cold storage’s offline nature provides fundamental protection.
Multi-signature cold storage represents the gold standard for institutional cryptocurrency security. This approach requires multiple private keys—often distributed across different locations and holders—to authorize any transaction. Major cryptocurrency custodians like Fidelity Digital Assets and BNY Mellon employ multi-signature cold storage with geographic redundancy, ensuring that no single point of failure can compromise client assets.
How to Choose the Right Wallet
Selecting between hot and cold storage—or more likely, a combination of both—requires honest assessment of your specific situation, technical comfort level, and cryptocurrency use patterns.
Choose Hot Storage If:
You actively trade cryptocurrency, need immediate access for purchases or transfers, hold amounts you can afford to lose, and prioritize convenience over maximum security. Most users should keep only small amounts in hot wallets—enough for immediate needs but well within what they could absorb losing.
Choose Cold Storage If:
You hold cryptocurrency as a long-term investment, store significant value, prioritize security over convenience, and can safely store physical devices or documents. Cold storage suits anyone holding more than a few hundred dollars in cryptocurrency that they don’t need for daily transactions.
The Layered Approach:
Most experienced cryptocurrency holders employ multiple wallet types simultaneously. Keep working capital in a hot wallet for accessibility, store medium-term holdings in a hardware wallet, and maintain long-term hodlings in the most secure cold storage available. This layered approach balances security against accessibility based on your specific needs.
Setting Up Your First Wallet
Regardless of which wallet type you choose, proper setup significantly impacts your security posture. Taking time to understand and implement security best practices from the beginning prevents costly mistakes later.
Initial Setup Steps:
1. Purchase hardware wallets directly from manufacturers—never from third-party sellers
2. Create strong, unique passwords stored in a password manager
3. Write down seed phrases on paper or steel, making multiple copies stored in separate secure locations
4. Verify your backup works by restoring to a fresh device or software installation
5. Test small transactions before transferring significant amounts
6. Enable all available security features including two-factor authentication where applicable
Common Mistakes to Avoid
Cryptocurrency wallet mistakes can prove irreversible, making prevention essential. Learning from others’ errors helps you avoid becoming another cautionary tale in cryptocurrency security discussions.
Mistake #1: Storing Seed Phrases Digitally
Saving your seed phrase in email, cloud storage, or text files creates vulnerabilities that defeat cold storage’s security purpose. Hackers routinely scan for exposed seed phrases, and any digital copy can be stolen remotely. Physical backups stored securely remain the only recommended approach.
Mistake #2: Neglecting Multi-Factor Authentication
Even hot wallets with strong passwords can be compromised through SIM-swapping attacks or data breaches. Enable multi-factor authentication on all accounts, preferring hardware security keys over phone-based authentication when possible.
Mistake #3: Not Verifying Addresses
Cryptocurrency transactions cannot be reversed. Always verify receiving addresses character-by-character, especially when copying from chat applications or websites that might have been compromised. Attackers frequently substitute addresses in communications, a scam that has cost victims billions.
Future of Cryptocurrency Storage
The cryptocurrency wallet landscape continues evolving rapidly, with new solutions addressing longstanding security and usability challenges. Multi-party computation (MPC) technology now enables institutional-grade security without single points of failure, distributing key fragments across multiple parties or devices. Companies like Fireblocks and BitGo have popularized MPC wallets among institutional users.
Social recovery options provide backup mechanisms without single points of failure. Rather than a single seed phrase that can be lost or stolen, social recovery allows designated trusted contacts to collectively restore access to your wallet. This approach addresses one of cryptocurrency’s most challenging problems: the permanent loss of funds when keys disappear.
Self-custody solutions are also becoming more user-friendly, with leading hardware wallets introducing touchscreens, mobile apps, and simplified recovery processes. The tension between security and accessibility continues driving innovation, with each generation of products finding better balances.
Conclusion
Understanding the distinction between hot and cold storage represents fundamental knowledge for any cryptocurrency holder. Hot wallets provide essential accessibility for active trading and frequent transactions, while cold storage delivers the security necessary for protecting significant value. Rather than choosing exclusively between the two approaches, most users benefit from employing both—keeping accessible working capital in hot storage while securing long-term holdings in cold wallets.
The specific wallet types you choose matter less than implementing proper security practices consistently. Enable two-factor authentication, maintain secure backups of seed phrases, verify all transaction addresses, and remain vigilant against phishing attempts. As the cryptocurrency ecosystem matures, those who prioritize security while maintaining practical accessibility will best position themselves to benefit from this transformative technology.
Frequently Asked Questions
What is the safest cryptocurrency wallet type?
Hardware wallets that store private keys offline represent the safest option for most users. Devices like Ledger and Trezor keep keys isolated from internet-connected computers and phones, protecting against remote attacks. Multi-signature cold storage provides even greater security for large holdings or institutional assets.
Can I use both hot and cold wallets simultaneously?
Yes, most experienced cryptocurrency holders use multiple wallet types. A common strategy keeps small amounts in hot wallets for daily transactions while storing larger holdings in cold storage. This layered approach balances security against accessibility based on your specific needs.
Do I need a hardware wallet if I only hold a small amount?
While hardware wallets provide superior security, they involve costs and learning curves that may not justify their use for very small amounts. If holding less than you can comfortably afford to lose, a reputable hot wallet may suffice. However, hardware wallets remain worthwhile once your holdings exceed a few hundred dollars.
What happens if I lose my hardware wallet or forget my password?
Your seed phrase serves as the ultimate backup. If you lose a hardware wallet, you can restore access by entering your seed phrase into a new device. Without the seed phrase, recovery becomes impossible—which is precisely the security feature that protects your funds from attackers.
Are exchange wallets safe for storing cryptocurrency?
Exchange wallets are hot wallets controlled by third parties, making them vulnerable to platform hacks and insolvency. The collapse of FTX, Mt. Gox, and other exchanges demonstrates the risks of leaving cryptocurrency on trading platforms. For any amount you cannot afford to lose, self-custody in your own wallet remains the safer approach.
How do I transfer cryptocurrency from a hot wallet to a cold wallet?
Initiate a withdrawal from your hot wallet by entering your cold wallet’s public address. Always verify the address character-by-character before confirming, as addresses cannot be reversed once sent. Start with a small test transaction before moving significant amounts to confirm everything works correctly.






Leave a comment